Russian Railways (OJSC “RZD”) is the steel bloodstream of war, sustaining the Russian occupation forces in Ukraine. Today, as the intensity of hostilities in eastern and southern Ukraine requires the uninterrupted delivery of hundreds of thousands of tons of ammunition, armored vehicles, and personnel, the Russian Federation’s railway network is operating at the limit of its capacity. Yet, as the seized volumes of internal corporate documentation show, this bloodstream is deeply infected by systemic corruption, personnel shortages, technological hunger, and, most importantly for Ukrainian security, hidden vulnerabilities that make it possible to disguise the movement of military echelons as “technical failures.”

This investigation, conducted on the basis of a dataset containing terabytes of internal accounting records, maintenance reports, correspondence, and financial statements (for the period 2024–2026), exposes the critical failure points of Russian Railways. The Institute KRONOS received this information from the “Hacker Cat” community for analysis and subsequent publication. The materials became available thanks to a brilliant hacker operation, as a result of which we obtained comprehensive data, while OJSC “RZD” lost access to this information. We deconstruct, step by step, the corrupt hierarchy, analyze mysterious automation failures at key stations of the Moscow transport hub, trace shadow channels for sanctions evasion in the procurement of Western microelectronics, and expose the mechanisms of payments for the so-called “SVO” on the strategically important Voronezh direction.
The documents obtained constitute a ready-made evidentiary base for sanctions lists and, at the same time, an invaluable map of vulnerable nodes that are already primed for “accidental” or coordinated catastrophes. Our objective is to demonstrate how Ukraine can exploit these vulnerabilities to turn the enemy’s logistical advantage into its greatest weakness.
FINANCIAL PARASITISM BASED ON “ASU SERVICE” AND “ELTEZA”
To understand why Russian Railways is becoming increasingly vulnerable to cyberattacks and physical sabotage (such as arson attacks on relay cabinets), it is sufficient to examine how the maintenance of its most complex systems is financed and distributed — microprocessor interlocking (MPC) and rolling stock technical condition monitoring systems (KTSM).
KTSM are the eyes of the railway. They scan passing trains for axle-box overheating (bearings). If KTSM fails, the risk of derailment rises exponentially. MPC is the brain of the station, controlling points and signals. Instead of direct, transparent financing of these critical elements, RZD uses a multi-layered corrupt model aimed exclusively at accumulating financial rent.
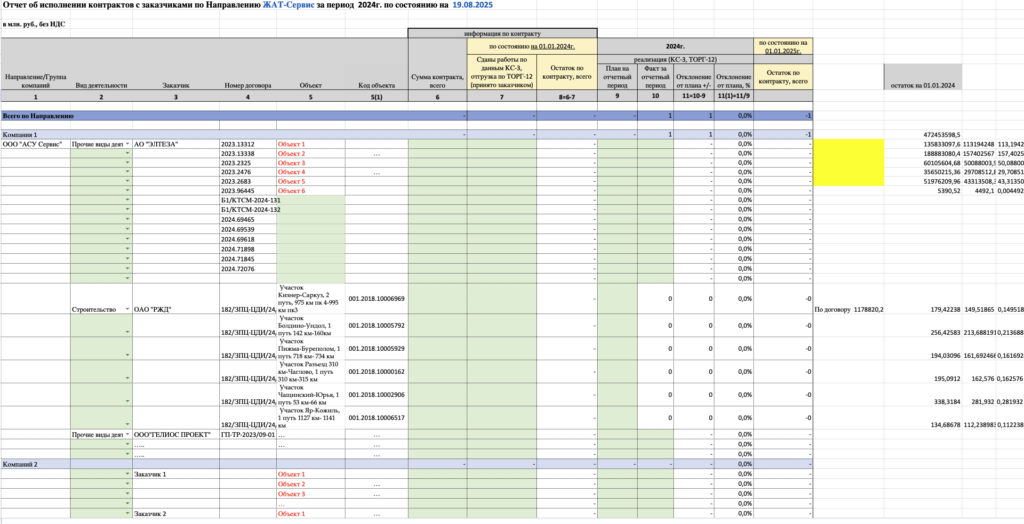
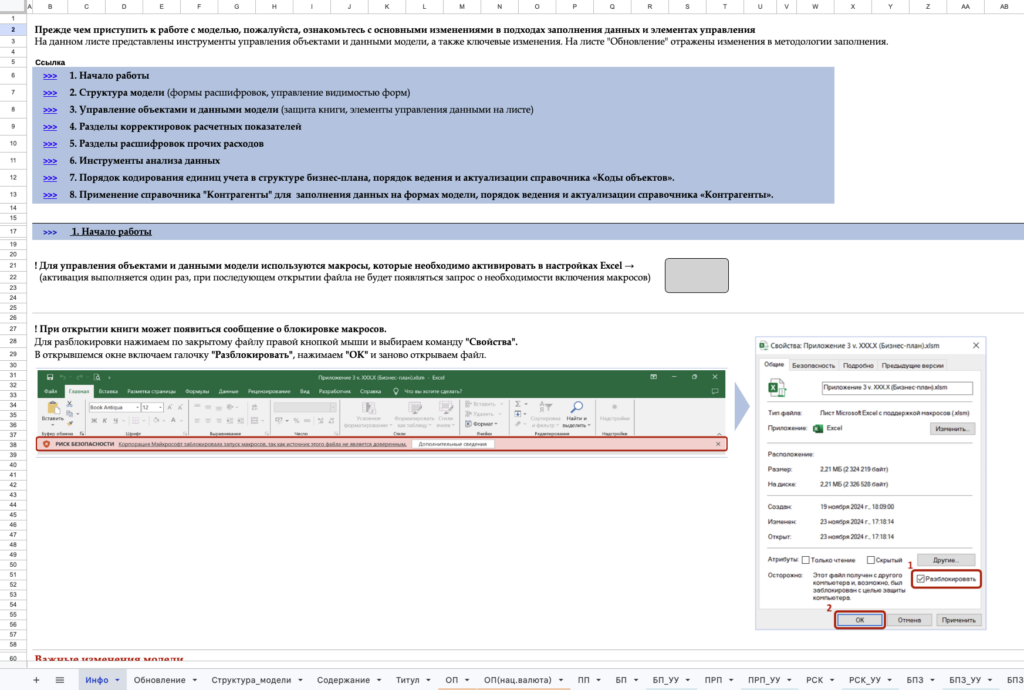
We conducted a deep analysis of the file `Шаблон_Реестр контрактов_2024 (3).xlsx` and the colossal document `Приложение 5. Отчет об исполнении бизнес-плана за 9 месяцев 2025 года .xlsm`. These documents clearly reveal a hierarchical structure of financial parasitism:
1. Customer: OJSC “RZD” represented by the Central Infrastructure Directorate (CID).
2. General contractor: JSC “ELTEZA.” (A company in which, apart from RZD, private shareholders and oligarchic holdings that monopolized automation production play a key role).
3. First-tier subcontractor: LLC “ASU Service” — the organization to which the lion’s share of maintenance work on complex systems at hundreds of stations is formally assigned.
4. Lower tiers (actual executors or “buffers”): LLC “Sector,” LLC “SZSA,” “TEPLOSTROY,” and other small regional firms.
In the document we studied, `ОСВ по счету 60.01 за 2025 г..xls` (“trial balance”), striking cash turnovers are recorded. Account 60 in Russian accounting is used for settlements with suppliers and contractors. Thus, LLC “Sector” processed more than 9.2 million rubles through itself in an extremely short reporting period (balance: 1.16 million rubles). At the same time, a colossal 29.7 million rubles passed through LLC “SZSA” (considering the narrow niche of automation repair services).
But is the involvement of these third parties justified when the technical capabilities of “ASU Service” itself or directly “ELTEZA” are available?
The answer is an unequivocal no. Internal documentation, including complaints and correspondence from branch management, indicates that most of the work nominally transferred to LLC “Sector” or LLC “SZSA” is in fact performed by regular, low-paid teams of “ASU Service,” and sometimes directly by RZD’s own electrical mechanics (ShN). The existence of these specially created intermediary companies is a textbook scheme of inflating estimates and withdrawing state funds into the shadows through fictitious completion certificates (F-2, KS-3).
The margin on operations is artificially inflated by 30–40% at each stage of delegation. This is also confirmed by the fact that in detailed payroll records (according to the file `Расшифровка ФОТ за 2025 год…xls` and `Расшифровка старшие эл.механики.xlsx`) the actual wage fund of the direct engineers — senior electrical mechanics, first-category engineers — is minuscule and does not correspond to the contract value of the work. The people who physically solder wires in the snowstorm and replace switching boards receive crumbs, while millions settle in the accounts of LLC “SZSA.”
Conclusion on the hierarchy: This system creates a critical, arguably the most important, vulnerability for Russian infrastructure. The “buffer” companies bear no real criminal or technical responsibility for traffic safety and cannot bear any such responsibility.
In the event of a serious accident, sabotage, or a false point activation that leads to an echelon catastrophe:
* OJSC “RZD” shifts responsibility to the general contractor — JSC “ELTEZA.”
* “ELTEZA” produces documents showing that maintenance was delegated to LLC “ASU Service.”
* The management of “ASU Service” shrugs and presents signed transfer certificates for this specific facility to LLC “Sector.”
Irresponsibility becomes systemic, cascading, and intractable.
THE GHOSTS OF CHERKIZOVO STATION: HOW “TECHNICAL FAILURES” HIDE MILITARY ECHELONS
One of the most intriguing and alarming signals in the entire seized dataset was found in a specially designated folder titled `Cherkizovo`. It contains documents marked for internal use: `Тех заключение МЦК 5.05 ЦШ.pdf`, `Претензия Черкизово 10247.pdf`, and `Письмо 1520 Сигнал 1857-АБ.PDF`, describing mass, allegedly cascading failures of microprocessor interlocking (MPC) systems at Cherkizovo station on 3 and 5 May 2025.
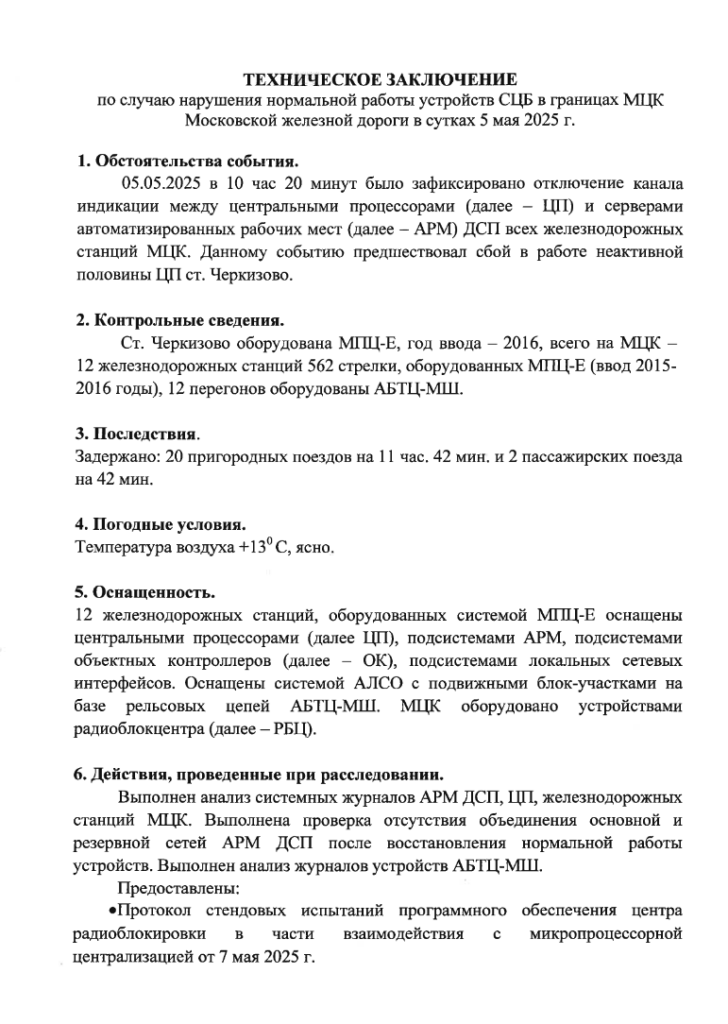
Cherkizovo is a critical transit node of the Moscow Central Circle (MCC), which, through a system of connecting junctions, provides freight and transit connections between several strategic main lines, bypassing congestion at central stations.
The official version of the failure, as follows from the “technical conclusion” and the claims sent to the software developers, is a “sudden software failure,” “loss of communication between upper- and lower-level controllers,” and “freezing of the station duty officer’s interface.” However, a deep OSINT analysis of traffic schedules, open data, and internal directives (including direct references to “lettered” trains in `БП КТСМ АСУ кбш 2025 в работе.xlsx`) points to a completely different, far more sinister nature of these so-called “failures.”
The term “lettered” (literny train) in Soviet and modern Russian railway tradition refers to a train of special, primarily military or government purpose, which has absolute and unquestionable priority. These may include:
1. Trains carrying ballistic missiles or nuclear materials.
2. Echelons of heavy armored vehicles being transferred from Siberia or the Urals to the Ukrainian front.
3. Armored special trains of the top military-political leadership of the Russian Federation (including Putin’s personal armored train).
Such trains move under maximum secrecy, outside the normal, rigid timetable. In order to safely and without stops pass a “lettered” consist through the highly strained and dense traffic of the Moscow hub (where the interval between “Lastochka” trains is measured in minutes), the dispatch system requires radical manual intervention.
However, modern microprocessor traffic control systems (MPC-EL, Ebilock, and others) are designed to eliminate the “human factor.” They rigidly and reliably log (record in an immutable archive) absolutely all manual route cancellations or signal blockages.
What do we see when we compare the dates and context of the incident in Cherkizovo?
1. Temporal context: The first days of May are a period of intensive preparation for militaristic “parades” in Moscow (the transfer of equipment within the Moscow garrison), as well as the traditional spring replenishment of strategic reserves for the spring-summer campaign in Ukraine.
2. Mechanics of the failure: Instead of running echelons through the MCC officially, thereby violating all civil logging systems, the MPC system “unexpectedly” and “conveniently” goes down. A so-called “black screen” appears on the dispatcher’s workstation (shutdown of the display on the duty officer’s monitors).
3. Switch to manual control: The MPC failure automatically allows, and indeed forces, dispatchers, in accordance with regulations, to switch to manual control of points and signals by telephone and radio. At that moment, the system’s automatic technical log is destroyed or halted. The movement of the “lettered” consist is almost not recorded in the centralized database of RZD’s Main Computing Center (GVC) as a single route, since the station is officially “in emergency fault-removal mode.”
This is not a software bug. It is a systematic, well-practiced method of concealing military logistics under the guise of software or hardware failures in MPC. Our investigators are convinced that the management of contractor companies such as “ASU Service” fully understands the real nature of these false “failures.” Their function is reduced to silently signing a pre-prepared fictitious act stating that the board “froze due to static voltage,” and later receiving funds for its “diagnostics and repair.”
This approach by the FSB and military commandant’s offices has catastrophic side effects for RZD itself. When dispatchers are regularly trained to ignore automation and, on command, switch a station into “emergency” mode to let “ghosts” through, the system loses its instinct for self-preservation. This fact enables Ukrainian forces to strike at the moment of such artificial “shutdowns” — because at that time the station is most vulnerable, “blind,” and any anomaly will be perceived by local personnel as yet another whim of the FSB.
LOSTA STATION: 5 MONTHS OF DOWNTIME AND INFRASTRUCTURAL PARALYSIS
An obvious, indisputable proof of the rapid degradation of the maintenance system is the angry correspondence found in the file `Письмо АСУ-Сервис по неустранённым иинцидентам ОКТ. ДИ (1).pdf`, as well as in related reports concerning the stations of Redkino and Vaskelovo (`Письмо по ст. Васкелово Окт. ДИ.pdf`). The documentation reveals a picture of complete administrative and technical collapse at a number of the most important stations of the October and Northern Railways.
The most symptomatic and illustrative case is that of Losta station. Losta is a giant hub sorting station of the Vologda hub on the Northern Railway, a key artery connecting Russia’s industrial center with the northern ports and Trans-Siberian routes.
According to official complaint reports, at Losta station the waiting time for repair of the basic rolling stock diagnostics complex (presumably the KTSM complex or its communication interfaces) exceeded a colossal 5 months. Let us reflect on these figures: for nearly half a year, one of the country’s most important sorting hubs operated “blind” or in gross, persistent violation of the Rules for Technical Operation (PTE), simply sending trains through at random.
An analysis of estimates and internal correspondence reveals two parallel, deeply rooted causes of such unprecedented delays:
1. Artificially created shortage of spare parts (SP). Money for parts and hot standby units is regularly allocated, but it settles in the transit accounts of LLC “Sector” or LLC “SZSA” (whose scheme we analyzed in section 1). Without a real physical pool of spare microchips, memory modules, or basic industrial power supplies, local mechanics are left in a hopeless situation. They simply have nothing with which to physically replace boards burned out by voltage surges.
2. Creeping sabotage at the grassroots level. We record a clear trend toward an increase in refusal reports from senior mechanics (ShNS). The old-school engineering staff refuses to assume potential criminal liability (and railway disasters in the Russian Federation are punished harshly) for releasing into service improvised, hand-soldered safety devices. Therefore, the 5-month delay is also a form of institutional “Italian strike.” Workers act strictly according to instructions: “No officially certified part from the general contractor’s warehouse? Then the station or complex will stand until the victorious end.”
For Ukrainian specialists in kinetic and cyber effects, this document is an important targeting cue: the Russian railway network has completely lost its buffer capacity and resilience. A failure of even the smallest switch at a hub station now does not lead to an operational response and repair within 4 hours (as was stipulated 5 years ago). Today, any failure leads to a logistical collapse lasting months because of the deep bureaucratic and corrupt paralysis of the Russian vertical.
Any, even the simplest, low-tech sabotage act (for example, a thermite fire on a specific relay cabinet on a line section, or mechanical damage to a cable duct) at stations of Losta’s structural level will guaranteedly take that section out of automatic mode for a period of 3 to 6 months. Rapid restoration is physically impossible, because the electronics supply chain has been plundered and buried under paperwork of “deferred demand.”
HOW INTEL AND MOXA CHIPS LEAK THROUGH SANCTIONS TO RZD
This section of our investigation focuses on one of the main myths of Russian propaganda — total import substitution in critical infrastructure. The key factor explaining the 5-month downtime at stations is the categorical shortage of foreign electronic component base (ECB), which Russia does not produce.
Modern microprocessor interlocking systems (MPC-EL and its derivatives), developed and implemented by “ELTEZA” years earlier, are conceptually dependent, at the level of low-level architecture, on Western components. In particular, these include industrial controllers manufactured by Intel, protected switches from the famous Taiwanese company Moxa, without which no industrial station communication network functions, as well as server farms running on Texas Instruments semiconductors and Cisco systems.
Under a tightly controlled global sanctions regime, direct official procurement of these specific parts for the needs of “RZD” (especially for military transport) is practically impossible. Therefore, so-called “offshore vacuum cleaners” enter the scene — special transit shell companies whose sole purpose is to mask the end user (End User). In our dataset, one such key shadow company clearly surfaced: LLC “ALGORITHM OF SECURITY” (TIN 7709793338), as well as the affiliated LLC “TK ALGORITHM.”
In the multi-page giant file `Приложение 5. Отчет об исполнении бизнес-плана за 9 месяцев 2025 года .xlsm`, this company appears in multi-million-ruble entries under “external procurement.” “Algorithm” acts not so much as a developer of security systems (as stated in its charter) but rather as an aggressive gray importer.
An analysis of their financial activity and ties to general contractors clearly shows that they systematically, using complex logistics chains, massively purchase industrial routers and transceivers from Asian electronics hypermarkets (mainly through special hubs in mainland China, Hong Kong, Kazakhstan, and Turkey). These parts are absolutely necessary for restoring KTSM systems (axle-box and brake temperature monitoring), and they are resold to LLC “ASU Service” under the guise of “general-purpose components” or deeply concealed within finished, formally “Russian” iron modules.
In other technical replacement reports (we examined the folder `письмо о замене УКТРЦ-8, ПИК-10 и ПИК-120.pdf`), we observe schemes in which old control units are legalized with new chips, the provenance of which is carefully erased from maintenance documentation.
The large-scale legalization of imports through “TK ALGORITHM” and “ALGORITHM OF SECURITY” is a textbook, dirty scheme for circumventing Western sanctions. The information we found is more than sufficient grounds for the immediate inclusion of the legal entities and individual founders in OFAC secondary sanctions packages (U.S. Department of the Treasury), as well as the relevant sanctions lists of the EU and Ukraine’s National Security and Defense Council.
The application of targeted secondary sanctions against these specific shell companies will finally block their access to the Chinese and Taiwanese semiconductor markets, since Asian Moxa distributors are extremely afraid of falling under U.S. sanctions. Once “Algorithm” is paralyzed by Western financial monitoring, repair times at Russian stations such as the aforementioned Losta will turn from 5 months into eternity, since they will simply have nothing physically with which to solder the burned-out logic matrices of signaling nodes.
THE VORONEZH LOGISTICS HUB AND “SVO” IN PAYROLL RECORDS
A particularly, I would say exclusive, place in the analyzed dataset is occupied by accounting and personnel documentation for the Voronezh hub and the Southeastern Railway of the Russian Federation. This region is geographically key, the largest logistics hub for the entire Russian grouping of occupation forces on the Slobozhansky and partly Donbas directions in Ukraine. Thousands of tons of ammunition and equipment pass through Voronezh every month. Accordingly, maintaining automation here is literally a matter of survival for the Russian army.
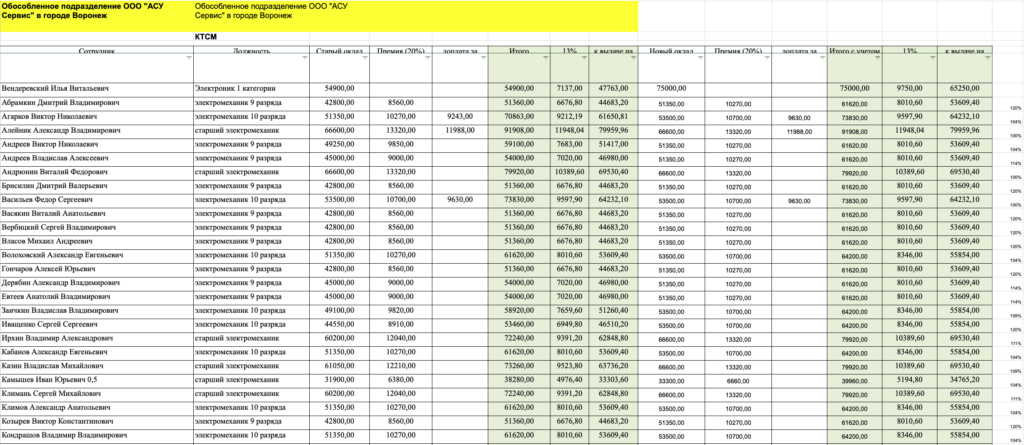
In the seized files `КТСМ ФОТ .xlsx` (which contains detailed, down to the kopeck, payroll calculations for the brigades of Voronezh, Samara, and Saratov), as well as in special bonus statements (the most glaring example: `Премия ЮВДИ июль 2025.xlsx`), we found numerous specific markings referring to payments for work in special, military conditions. The abbreviation “SVO” regularly appears in explanatory notes and in the columns justifying increased rates.
As became clear during a deep cross-referencing of the tables, a significant portion of the qualified engineers, line mechanics, and section supervisors of LLC “ASU Service” in the Voronezh region are formally employed in a peculiar “voluntary-compulsory” manner (concealed behind specific contracts) to carry out urgent restoration work on the tracks. They work not only in the deep rear but also in directly border regions (Belgorod, Kursk, Voronezh), and are also likely sent on so-called business trips to the temporarily occupied territories of Ukraine (Luhansk region, restoration of lines to Starobilsk, etc.).
The Voronezh payroll tables and related personnel records unambiguously indicate the following facts:
1. Local civilian personnel in practice perform the functions of emergency “rapid response” battalions of railway troops — they repair tracks and automation after rails damaged by Ukrainian groups and kamikaze drone strikes.
2. The accounting system reveals mass hidden supplements. To pass this money “on the books” through the Russian tax service and minimize unnecessary questions, the management of LLC “ASU Service” issues material “combat” incentives disguised as an inflated bonus fund. Their real purpose is to compensate for the risk of being killed by cluster munitions near Belgorod.
3. The duty rosters (in particular in the files `Список ОП Воронеж по участкам (1).xlsx`, `График дежурств (общий) (1).xlsx`) openly list full names, personal mobile phone numbers, and the exact zones of direct infrastructure responsibility of the engineering staff.
SYNTHESIS OF VULNERABILITIES
For the convenience of planning further disruptive and sanctions-related measures, all key markers have been consolidated into a single analytical matrix of vulnerabilities in the management and support system of OJSC “RZD.” The synthesis below is based exclusively on the documents:
ANALYTICAL LINK TABLE: MARKERS OF CORRUPTION, SABOTAGE, AND SANCTIONS EVASION
| Object / Organization | Role / Function | Characteristics / Vulnerabilities | Sources / Documents | Methods of Influence / Exploitation |
|---|---|---|---|---|
| OJSC “RZD” | Customer of automation systems and infrastructure holder. | Systemic cash-flow delays in payment; delegation of critical safety to third, unqualified parties. Uncontrolled and prolonged failures on regional sections; pathological inefficiency. | Trial balance on account 60.01 for 2025.xls, various complaint letters. | Exploitation of cash-flow gaps; attacks on the corporate payment processing system to provoke engineer strikes and salary delays. |
| JSC “ELTEZA” | General contractor for MPC/KTSM development. | Orientation toward superprofits through the use of foreign imported component base (ICB), which they are unable to replace independently under global restrictions. | БП КТСМ АСУ кбш 2025 в работе.xlsx, registry templates. | Secondary hard sanctions against their oligarchic founders and subsidiaries; massive cyberattacks on internal ERP systems and file servers, encryption of development backups. |
| LLC “ASU Service” | Main subcontractor and front office. | The ideal “buffer” that distributes funds and forms shadow “combat bonuses” for SVO. Knowingly and obediently conceals the movement of military equipment and sabotage under fictitious technical failures. | КТСМ ФОТ .xlsx, Приложение 5…, Премия ЮВДИ июль 2025.xlsx. | De-anonymization of all line personnel (Voronezh payroll, OCT DI). |
| LLC “Sector” / LLC “SZSA” | Lower tier of subcontracting (buffers). | Parasitic firms for cash extraction and inflating maintenance estimates by tens of times. They process tens of millions of rubles without having real production bases on site. | Шаблон_Реестр контрактов_2024 (3).xlsx. | Freezing of bank accounts as a result of identifying their counterparties; tracing and investigating the property of their ultimate beneficiaries in Europe (with subsequent arrest). |
| Cherkizovo station (MCC) | Strategic transit hub of Moscow. | Mass, artificial collapses of “MPC” systems (notably on 03.05.2025 and 05.05.2025). Concealment of the movement of unscheduled military consists of elevated priority “lettered” trains under the cover of hacking or software problems. | Тех заключение МЦК 5.05 ЦШ.pdf, Претензия Черкизово 10247.pdf. | Identification of the exact schedule of special consists by monitoring the time of MPC software “failures.” Cyberattacks on the MCC computing center precisely during such “manual” switches. |
| Losta station (Northern Railway) | Giant hub sorting station. | Waiting for warranty repair and spare parts for the automation complex for more than an unprecedented 5 months. Mechanics’ “Italian strike” on site due to a systemic shortage of spare parts. | Письмо АСУ-Сервис по неустранённым иинцидентам ОКТ. ДИ.pdf. | Carrying out minor physical actions on Losta relay cabinets — the station will go down for 5+ months by a completely “natural” route, with no chance of rapid hardware restoration. |
| LLC “ALGORITHM OF SECURITY” | Shadow importer of sanctioned technologies. | Procurement of Intel components, Moxa switches, and Cisco servers through Turkey/PRC and their legalization for the technical re-equipment of Russian MPC and KTSM systems. | Приложение 5. Отчет об исполнении бизнес-плана за 9 месяцев 2025 года .xlsm. | Immediate, unconditional inclusion of the company and its residents (TIN 7709793338) in the OFAC and NSDC secondary sanctions list to cut off access to the chip markets of China and Taiwan. |
| Voronezh hub (Personnel) | Regional central hub for “SVO” support. | Payment of hidden “SVO” supplements disguised as bonuses for hazardous work by line engineers in border areas and in the occupied territories of Ukraine (Belgorod, Kursk, Luhansk). | Список ОП Воронеж по участкам (1).xlsx, График дежурств (общий).xlsx. | Public disclosure of personal data (direct phone numbers, full names) of mechanics from SVO brigades on special resources such as “Mirotvorets,” etc. |
CONCLUSIONS AND VERDICT
The fundamental OSINT analysis of the seized corporate dataset of the Russian “RZD” system unequivocally indicates deep, irreversible institutional pathologies that undermine the aggressor’s military-logistical potential from within better than any kinetic weapon. Russia’s railway is a colossus on clay, corrupt legs.
1. Total corruption-subcontracting ulceration (through the structures “ELTEZA,” “ASU Service,” “Sector,” “SZSA”) consumes up to half of the budget allocated to maintaining safety and traffic control systems every day. The railway automation of Russia’s main lines is sustained solely by the inertia of Soviet reserves of strength and by gray imports of dubious quality. This money is stolen from the very engineers who are supposed to ensure movement.
2. A new tactic for concealing military movements has been recorded and documented. Military “lettered” trains of elite priority at hub transit stations (such as Cherkizovo) are systematically concealed through artificially initiated “software failures.” This is a deliberate administrative deception that makes it possible to disable logging on central servers and pass echelons carrying weapons past civilian control in a retrograde manual telephone-control mode.
3. The agony of warehouse stocks (the Losta syndrome). The situation we identified at Losta station serves as indisputable proof that the supply chain on the Northern and October Railways is completely broken. The restoration time for critical automation has exceeded 5 months. In the event of targeted physical impact (sabotage by special forces or partisans), large sections of track will be paralyzed for at least half a year, with no possibility whatsoever of prompt replacement of boards and microcontrollers.
4. The Western smuggling corridor has been exposed. Sanctioned foreign-made components (such as Intel semiconductors, Moxa protected switches, Cisco routers) are legalized and laundered through a network of intermediary companies such as LLC “ALGORITHM OF SECURITY.” Blocking the international financial activity of such “buffers” through U.S. secondary sanctions is the least bloody and at the same time the only guaranteed way to stop the supply of quality electronics for RZD’s military logistics needs. Without Taiwan, their stations will become blind.
5. The network of “SVO emergency repair crews” has been de-anonymized. Engineers in Voronezh and other border sections are no longer abstract, anonymous repair technicians. They have been fully identified, their tax and financial manipulations involving shadow “combat bonuses” have been documented, and their direct mobile phone numbers and minute-by-minute duty schedules have been exposed. Everyone responsible for the rapid restoration of tracks after Ukrainian strikes now appears in databases.
This unprecedented comprehensive report demonstrates the fundamental fragility, vulnerability, and instability of Muscovy’s logistical rear. In their steel railway bloodstream, corruption and grassroots sabotage have circulated unhindered for years, waiting only for a minor, precisely calibrated push to turn the aggressor’s entire giant transport system into a global, unstoppable infrastructural thrombosis.
Further operational steps:
Immediately prepare a package of documents and transfer the materials concerning the activities of LLC “ALGORITHM OF SECURITY” to international partners for the immediate sanctions-based disconnection of these counterparties from the microelectronics markets of Taiwan and China.
Institute of Social Dynamics and Security KRONOS
The investigation actively used OSINT tools and artificial intelligence, in particular the Gemini and Grok models. OSINT methods made it possible to collect and analyze open data from various sources, including social networks, public databases, and web resources. Gemini provided in-depth analysis of textual data, pattern detection, and forecasting, while Grok, created by xAI, was used to process complex queries and generate precise conclusions based on large volumes of information. The combination of these technologies significantly accelerated the investigation process, improved the accuracy of the results obtained, and revealed connections that might have remained unnoticed by traditional methods.